INNSBRUCK, Austria, October 24, 2022 /CNW/ — The Windows Local Security Authority Subsystem (LSASS) service is one of the targets for cybercriminals when they launch targeted attacks on an organization’s network. In this blog post, we discuss the importance of this process for targeted attacks.

AV-Comparatives Test Results – LSASS Credential Flush Security
From an attacker’s perspective, the LSASS process on a Windows machine is often critical to obtaining useful credentials from domain users and using them to move laterally within the targeted network. There are several different methods, including custom-designed malware, that can be used by attackers and red teams to extract credentials from the LSASS process.
LSASS Credential Flush Protection Depending on the security product installed and the applicable policy, it may be more or less easy for an attacker to obtain Windows user credentials by flushing the address memory of LSASS.
Some security products include specific hardening measures to protect the LSASS process and prevent credential flushing. However, it is not always possible to use these more restrictive policies in certain organizations’ environments, as they may cause problems with certain legacy applications or applications that are not well programmed. Therefore, IT administrators are advised to test a product’s hardening settings to see if they have any unwanted side effects.
Additionally, blue teams should always assume that determined attackers will find a way to flush the LSASS process, even if installed security products use specific code to harden the LSASS process against attacks. That is, they may still be able to extract user credentials from the LSASS process. In addition to specific LSASS hardening measures, security products can prevent credential flushing through, for example, the antivirus module; this can detect the malware being used or other files created by the malware, or use behavioral detection to block malicious actions. In some cases, the security product may not block the attack, but will at least produce an alert, warning the system administrator that malicious actions should be investigated.
Some enterprise security products have their LSASS hardening measures enabled by default. Examples are Avast Ultimate Business Security, Bitdefender GravityZone Business Security Enterprise, and Kaspersky Endpoint Detection and Response Expert. Microsoft also provides two features specifically used to protect the LSASS process, namely Protected Process Light (PPL) and Attack Surface Reduction (ASR) rules. PPL is enabled by default on Windows 11, but currently not on Windows 10; it is included in the Professional, Enterprise, and Education variants of Windows 10/11. ASR rules can be used in organizations’ networks in conjunction with Microsoft Defender and currently must be proactively configured on either operating system.
Testing Credential Flush Protection in Security Products
Given the importance of preventing the dumping of LSASS credentials, by May 2022 AV-Comparatives tested some enterprise security products to determine how well their hardening measures protected against attacks on LSASS.
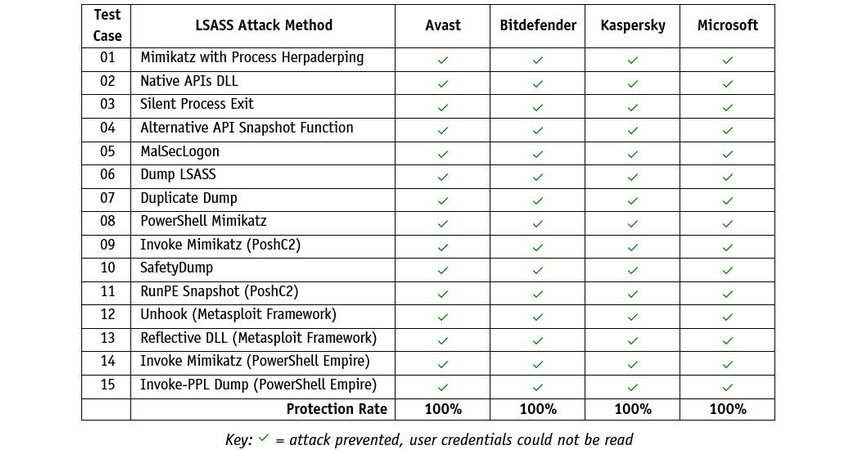
Below we list some examples of products (made by Avast, Bitdefender, Kaspersky and Microsoft) that showed effective protection against the 15 attacks used in our test, with their respective LSASS hardening measures enabled.
The table above includes results for the following products (with LSASS protection settings enabled): Avast Ultimate Business Security, Bitdefender GravityZone Business Security Enterprise, Kaspersky Endpoint Detection and Response Expert, and Microsoft Defender for Endpoint.
Microsoft asked us to post the results of an additional test of Microsoft Defender for Endpoint that we ran without their LSASS protection features (PPL and ASR) enabled. This was done to determine if the attacks listed above would be detected by other Microsoft security features. For each test case, AV-Comparatives checked whether the attack was correctly attributed to MITER ATT&CK tactics and techniques regarding LSASS in the event of detections or active alerts by the security product. In cases where the attack was prevented by the security product, the lab verified what threat information was provided in the management console. The methodology and other details of this test can be found in this PDF. For more information, please also read this blog entry from Microsoft.
E-mail: [email protected]
Telephone: +43 720115542
Contact: Peter Stelzhammer
Photo – https://mma.prnewswire.com/media/1927734/AV_Comparatives_LSASS_Table_Infographic.jpg
Logo – https://mma.prnewswire.com/media/1867361/AVC_Logo.jpg
SOURCE AV-Comparative

#AVComparatives #takes #deep #dive #LSASS #security